Introduction
Tactics, Techniques, and Procedures (TTPs) is an essential concept in terrorism and cyber security studies. The role of TTPs in terrorism analysis is to identify individual patterns of behaviour of a particular terrorist activity, or a particular terrorist organisation, and to examine and categorise more general tactics and weapons used by a particular terrorist activity, or a particular terrorist organisation.
Requirement to Identify Individual Terrorism TTPs
The current approach to terrorism analysis involves an examination of individual terrorist, or terrorist organisations use of particular weapons, used in specific ways, and different tactics and strategies being exhibited. Broadly, a wide range of TTPs have been exhibited historically by individual terrorist, or terrorist organisations worldwide.
Key Concepts
Evolution of TTPs
All terrorists, or terrorist organisations, worldwide historically have exhibited an evolution in TTPs. This can be as a result of:
- Changing circumstances;
- Resource availability; or,
- Changing ideologies, or ‘war-focus’.
In the case of the Taliban, their tactics have consisted primarily of guerrilla-style improvised explosive device (IED) attacks and small-arms ambushes against international and state-level security forces and interests, such as police checkpoints and military supply convoys. However, more recently Taliban TTPs have expanded to include mass casualty attacks by suicide bombers and other suicide attacks in order to undermine the current government.
Kill-Chain Model
The kill-chain model (KCM) is a conceptual tool used in terrorism analysis and studies. All terrorists’ or terrorist organisations’ TTPs form part of understanding the terrorist kill chain, which is the pattern of transactional activities, link together in order for a terrorist act to take place. Broadly, this involves describing the ‘hierarchy of tasks and sub-tasks that may be involved in the execution’, or in making a terrorist act happen. These can include the arrangement and sequence of activities a terrorist or terrorist organisation uses in planning, organizing, mobilizing, training, equipping and staging resources and operatives. These activities make up the terrorist or terrorist organisations’ modus operandi or ‘attack system’.
Four sets of steps make-up the full KCM:
- The first set of activities are the ‘attack preparation steps’. In terms of terrorism analysis, individual transactions, such as acquiring finances, acquiring expertise, acquiring materiel, munitions or capability, recruiting members, conducting reconnaissance, mission rehearsal, conducting an attack, have signatures that identify them as terrorist or criminal acts or are consistent with the operations of a specific individual, cell or group.
- The second set of activities are called the ‘execution timeline’. This identifies the timeline, along which the terrorist, or terrorist organisations various activities, leading up to an attack process flows time-wise.
- The third set of activities is identified as ‘targeting’. An individual or group would carry out some form of dedicated reconnaissance with the aim of identifying weaknesses in the site or operation; and with that information determine the best method of attack.
- The fourth set of activities is identified as the ‘planning stages’. These involve some type of planning activity embedded into the ‘kill chain’, and is part of the process of organising, mobilising, training, equipping, staging, collecting resources and operatives. These make up the terrorist or terrorist organisations’ modus operandi, or its system of attack.
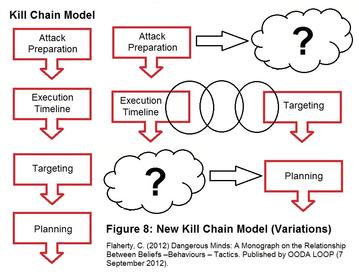
The KCM “sequence of activities” is not linear, but discontinuous. Three additional KCM scenarios can be identified:
- An individual or group actively promote a terrorist/extremist ideology on the internet, in books, pamphlets, etc. This is then picked up by another terrorist, or terrorist organisations, who then act on this.
- Two or more parallel kill chain sequence of activities (by various individuals/groups) which are only indirectly connected by intermediary individuals/groups. Sharing similar beliefs, but as well cross over into complementary beliefs/ideologies. Many such intermediaries can operate in this space, passing ideas and resources, even recruits between the various terrorist, or terrorist organisations, groups and cells.
- A terrorist or terrorist organisations picks up ideas, knowledge, etc., and jump-start into various places along the ‘standard’ concept of the KCM.
Transfer of Terrorist Tactics, Techniques and Procedures
Terrorist TTPs are often transferred between various terrorists, or terrorist organisations, and they often learn from each other. The degree to which the transfer of TTPs occurs depends on their relative success when transferred to a different conflict, and a different environment. The similarities in TTPs between various terrorists, or terrorist organisations, across conflicts and periods suggest a transfer of information.
- Explicit Knowledge: This is the theoretical information which is often stored in hard copies, such as textbooks, manuals and on computers through PDF and video files. These are extremely easy to get hold of, but without the appropriate teaching or experience, this easy access information is commonly not effectively used.
- Tactical Knowledge: Most commonly taught or learnt through experience and hands on teaching. This requires training establishments to be organised. For terrorists, or terrorist organisations, acquiring this information is harder, and more difficult; however, it is seen as a more effective transfer of knowledge.
Key Tactical Concepts Related to TTPs
Several key tactical concepts can be related to TTPs, which are typically used in terrorism or insurgency operations.
- Interposing tactics
- Mimicking operations
- Rhizome Manoeuvre
- Three-dimensional (3D) tactics analysis
- Swarming tactics
- Deliberate erratic actions, and erratic attacks
- Dynamic defence
This page is based on the copyrighted Wikipedia article < https://en.wikipedia.org/wiki/Terrorist_Tactics,_Techniques,_and_Procedures >; it is used under the Creative Commons Attribution-ShareAlike 3.0 Unported License (CC-BY-SA). You may redistribute it, verbatim or modified, providing that you comply with the terms of the CC-BY-SA.